nmap Network Reconnaissance
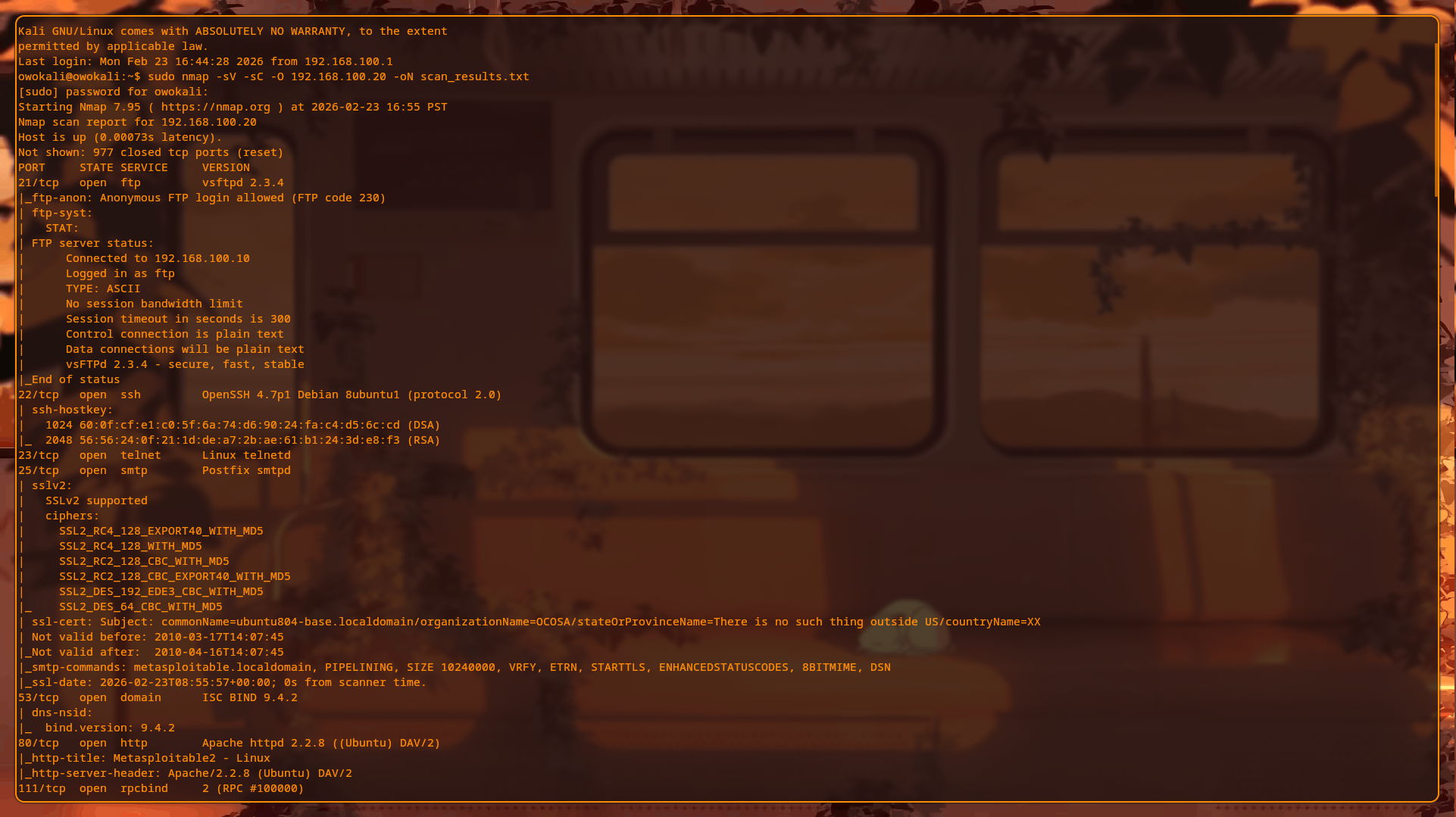
Full service and OS detection scan against Metasploitable2 (192.168.100.20) from Kali (192.168.100.10)
Summary
From the Kali attacker VM at 192.168.100.10, a full nmap service version and OS detection scan was run against the Metasploitable2 target at 192.168.100.20 on an isolated KVM homelab network. The scan completed in roughly half a minute and identified 23 open TCP ports exposing a wide attack surface of outdated, misconfigured, and intentionally vulnerable services.
- Multiple remote access services exposed, including FTP, SSH, Telnet, rsh/rlogin, VNC, and X11.
- Legacy application protocols and weak cryptography such as SSLv2 on SMTP and ancient OpenSSH.
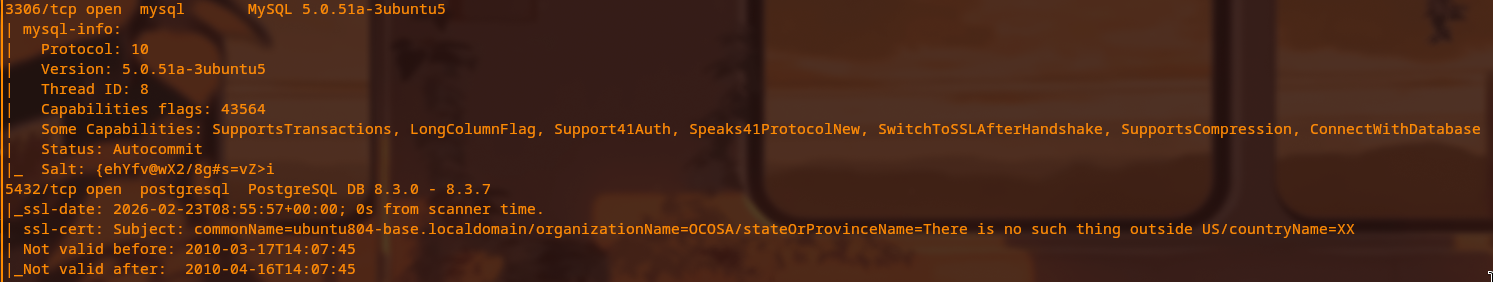
- Directly exposed databases (MySQL on 3306 and PostgreSQL on 5432) with no apparent network firewalling.
- Dangerous services like a root bindshell on 1524/tcp and Java RMI on 1099/tcp running without authentication.
Attack Technique Used
The attack technique here is classic network reconnaissance using nmap with service version detection (-sV), default script scanning (-sC), and OS fingerprinting (-O). This is the first phase of nearly every penetration test: systematically mapping reachable ports, identifying running services and versions, and inferring the underlying operating system in order to prioritize exploitation paths.
Steps to Reproduce
Terminal: Kali SSH (ssh owokali@192.168.100.10)
sudo nmap -sV -sC -O 192.168.100.20 -oN scan_results.txt
cat scan_results.txtComplete findings from scan:
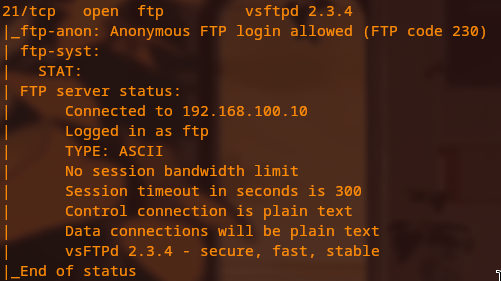
- Port 21/tcp: vsftpd 2.3.4 — anonymous FTP login allowed (FTP code 230), plaintext data connections, CVE-2011-2523 backdoor present.
- Port 22/tcp: OpenSSH 4.7p1 Debian 8ubuntu1 — very old SSH daemon from 2008, only supports deprecated key algorithms.
- Port 23/tcp: Linux telnetd — unencrypted remote access, all credentials and data sent in plaintext.
- Port 25/tcp: Postfix smtpd — SSLv2 supported (broken cryptography, DROWN-vulnerable), certificate expired April 2010.
- Port 53/tcp: ISC BIND 9.4.2 — outdated DNS server.
- Port 80/tcp: Apache httpd 2.2.8 — legacy web server with multiple known CVEs.
- Port 111/tcp: rpcbind — exposes NFS-related RPC services.
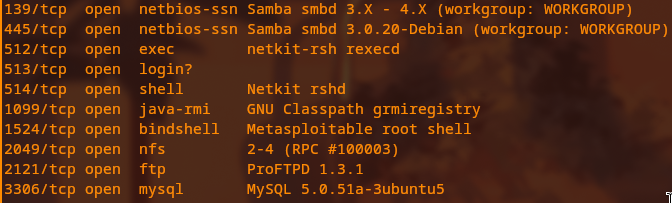
- Ports 139/tcp and 445/tcp: Samba 3.0.20 — SMB signing disabled, enabling relay-style attacks.
- Port 512/tcp: netkit-rsh rexecd — legacy remote execution service, no encryption.
- Port 513/tcp: rlogin — unencrypted remote login.
- Port 514/tcp: Netkit rshd — remote shell with no authentication or encryption.
- Port 1099/tcp: Java RMI GNU Classpath grmiregistry — unauthenticated Java RMI registry, later used for remote code execution.
- Port 1524/tcp: Metasploitable bindshell — preconfigured, unauthenticated root shell listener.
- Port 2049/tcp: NFS v2–v4 — network file system exposed directly.
- Port 2121/tcp: ProFTPD 1.3.1 — second FTP server instance.
- Port 3306/tcp: MySQL 5.0.51a — database exposed to the network with no firewall controls.
- Port 5432/tcp: PostgreSQL 8.3.0 — another database exposed directly to the network.
- Port 5900/tcp: VNC protocol 3.3 — remote desktop protocol exposed.
- Port 6000/tcp: X11 — display server exposed.
- Port 6667/tcp: UnrealIRCd — IRC server that is also known to ship with a backdoor in some versions.
- Port 8009/tcp: Apache JServ AJP — Java application server connector.
- Port 8180/tcp: Apache Tomcat 5.5 — Java web application server.
- OS detected: Linux kernel 2.6.9–2.6.33, roughly 2008-era; SMB security: message signing disabled (dangerous but default for this lab).
Detection (Wazuh)
Network scanning generates a large volume of short-lived connection attempts across many ports in a very small time window. In a monitored environment, Wazuh can flag this behavior: rule 5712 (or equivalent) triggers on repeated connection attempts and clear port-scanning patterns. In this lab the Kali host at 192.168.100.10 connected to every port on 192.168.100.20 within approximately 34 seconds, which is a textbook nmap scan signature that would also be visible to a network IDS such as Snort or Suricata.
Remediation
- Disable or remove all unused services — the initial attack surface was 23 open ports; hardened internet-facing systems should typically expose only a small handful of required services.
- Place databases (MySQL on 3306 and PostgreSQL on 5432) behind network firewalls or on internal-only VLANs; databases should never be directly reachable from untrusted networks.
- Replace Telnet, rlogin, and rsh with SSH everywhere to eliminate plaintext remote-access protocols.
- Apply current security patches to the operating system and all services; the 2.6.x kernel and software versions from 2008 have hundreds of publicly documented vulnerabilities.
- Implement network segmentation so critical assets (databases, domain controllers, SIEM infrastructure) reside on separate VLANs from exposed services.
- Disable anonymous FTP access and review all FTP usage; prefer SFTP or other encrypted file transfer mechanisms.
- Retire SSLv2 and other obsolete cryptographic protocols; enforce TLS 1.2+ with modern cipher suites.
MITRE ATT&CK Mapping
TA0043 Reconnaissance, T1046 Network Service Discovery, T1595 Active Scanning.
Screenshots with captions